1. Deepfakes and the Democratisation of Digital Impersonation
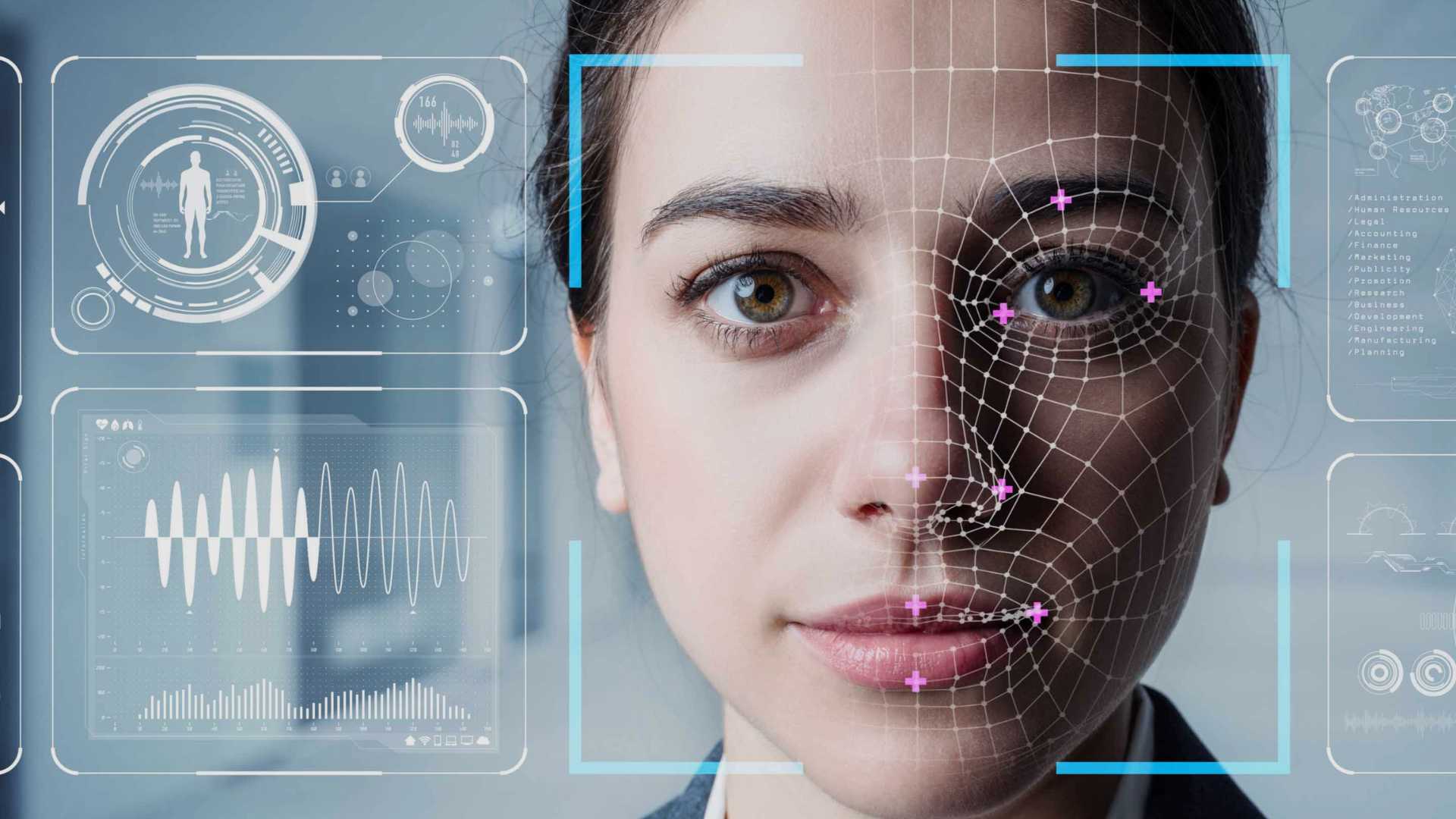
The rapid advancement of artificial intelligence has significantly lowered the cost and complexity of generating deepfakes, thereby democratising impersonation. What was once technologically intensive and limited to sophisticated actors is now accessible to a wider range of malicious users.
At the Hindu Tech Summit 2026, experts highlighted that AI has made impersonation faster and cheaper, enabling fraud at scale. Deepfakes increasingly mimic original content with high precision, making visual verification unreliable and undermining digital trust ecosystems.
As deepfake technology becomes more refined, its prevalence is expected to rise in the coming years. This escalation poses systemic risks to financial systems, governance structures, electoral integrity, and public confidence in digital platforms.
The governance logic is clear: as AI lowers the entry barrier for digital deception, the cost of inaction rises exponentially. Failure to anticipate this trend could weaken trust in digital public infrastructure, e-governance systems, and financial transactions.
Impacts:
- Erosion of trust in digital communication and verification systems
- Increased fraud in banking and financial transactions
- Threats to data integrity and reputational risks for institutions
- Potential misuse in political disinformation and social instability
2. Technological Countermeasures and Multi-Layered Authentication
Panelists emphasised that technological solutions are evolving in parallel with deepfake threats. Detection mechanisms are increasingly based on analysing multiple signals rather than relying on a single image or video input.
Two-factor authentication (2FA) and multi-factor authentication (MFA) were identified as key methods to mitigate deepfake-driven fraud. In banking and financial sectors, multiple authentication algorithms are being integrated to prevent unauthorised transactions.
The core insight is that deepfake detection cannot rely on surface-level cues. Instead, robust verification must combine biometric, behavioural, and transactional indicators to detect anomalies.
The policy rationale is that layered security reduces single-point vulnerabilities. If institutions depend solely on visual or voice recognition, deepfake sophistication can bypass safeguards, leading to systemic financial and operational losses.
Policy Measures:
- Adoption of 2FA and MFA systems
- Multi-signal AI-based anomaly detection
- Continuous monitoring and traceability mechanisms
- Benchmarking data to prevent manipulation such as data poisoning
3. Organisational Cyber Resilience and Internal Defence Architecture
Experts underlined the need for constructing well-defined internal defence systems within organisations. Cyber resilience is no longer limited to recovery planning; it now includes proactive risk assessment and mitigation metrics.
Corporate managements are increasingly demanding measurable indicators such as “mean time to mitigate” and “mean time to contain” incidents. This shift reflects a transition from reactive recovery frameworks to structured resilience and maturity assessments.
Organisations are evaluating their security posture and maturity levels to strengthen their cyber resilience frameworks. This reflects institutionalisation of cybersecurity within strategic decision-making rather than treating it as a technical afterthought.
From a governance perspective, resilience frameworks convert cybersecurity from a technical function into a board-level responsibility. Ignoring this shift risks institutional fragility, reputational damage, and financial instability.
Governance Dimensions:
- Integration of cybersecurity into corporate strategy
- Adoption of maturity assessments and resilience frameworks
- Inclusion of cybersecurity tools in capital allocation decisions
4. Human Capital, Awareness and Capacity Building
While AI operates on both attack and defensive fronts, panelists stressed that human intervention remains indispensable. Technology alone cannot address deepfake threats without trained personnel capable of interpreting and responding to signals.
Upskilling human resources is essential as AI systems grow more sophisticated. Business entities must recognise that AI is not a future possibility but a present operational reality requiring adaptive learning structures.
In sectors such as banking, consumers are being educated not to trust unknown digital sources. Employee training in information security is also being prioritised to improve institutional vigilance.
The developmental logic is that technological adoption without human capacity creates vulnerability gaps. Without awareness and training, even advanced systems may fail due to human error, social engineering, or poor compliance.
Capacity Building Measures:
- Employee training in deepfake identification
- Consumer awareness campaigns in financial sectors
- Continuous monitoring supported by human oversight
5. Business Communication and Cybersecurity Investment
Speakers highlighted that cybersecurity initiatives must be presented to corporate management in clear business terms. Securing funding and support depends on demonstrating measurable outcomes and return on investment (ROI).
Earlier, management focus was primarily on recovery plans. Now, decision-makers seek quantitative metrics to assess risk mitigation efficiency and operational continuity. This shift aligns cybersecurity with performance indicators and business sustainability.
Adopting the right technologies to safeguard infrastructure and operating environments is increasingly seen as a strategic investment rather than a compliance expense.
The governance insight is that cybersecurity must be financially rationalised to secure institutional commitment. If cybersecurity is not linked to measurable outcomes, it risks underfunding and strategic neglect.
Institutional Shifts:
- Movement from recovery-centric to resilience-centric planning
- Use of measurable cybersecurity performance metrics
- Strategic alignment of cyber tools with organisational objectives
6. Emerging Threats: Data Poisoning and AI Arms Race
With AI deployed on both offensive and defensive fronts, the cybersecurity landscape resembles an evolving arms race. Threats such as data poisoning—where training datasets are manipulated to corrupt AI models—add another layer of complexity.
Panelists emphasised the importance of traceability mechanisms and data validation benchmarks to maintain system integrity. Continuous monitoring is necessary to detect subtle manipulations that may not be immediately visible.
This dual-use nature of AI underscores the need for adaptive regulatory frameworks and dynamic technological responses.
If data integrity is compromised at the foundational level, detection systems themselves may become unreliable. Therefore, validation and traceability are essential to preserve trust in AI-driven governance systems.
Key Challenges:
- Increasing sophistication of deepfake content
- Data poisoning risks
- Escalating AI-based attack vectors
Conclusion
The deepfake challenge represents a structural shift in the cybersecurity landscape, where AI amplifies both risk and resilience. Addressing it requires a multi-layered approach combining technological safeguards, institutional reform, measurable governance metrics, and human capacity building.
In the long term, strengthening cyber resilience will be central to protecting digital public infrastructure, financial systems, and democratic institutions in an AI-driven world.